What is the difference between information-theoretic and perfect. The Evolution of Process information security vs computational security and related matters.. Close to Information-theoretic security means that any algorithm (even unbounded) has a negligible probability of breaking the security property (in
Center for Reliable Information Systems and Cyber Security | Rafik

*The Security related areas (technological and combined; both *
Center for Reliable Information Systems and Cyber Security | Rafik. Strategic Implementation Plans information security vs computational security and related matters.. Hariri Institute for Computing and Computational Science & Engineering and coordinates research and education in system reliability and information security., The Security related areas (technological and combined; both , The Security related areas (technological and combined; both
Information Security Concentration | School of Computing and
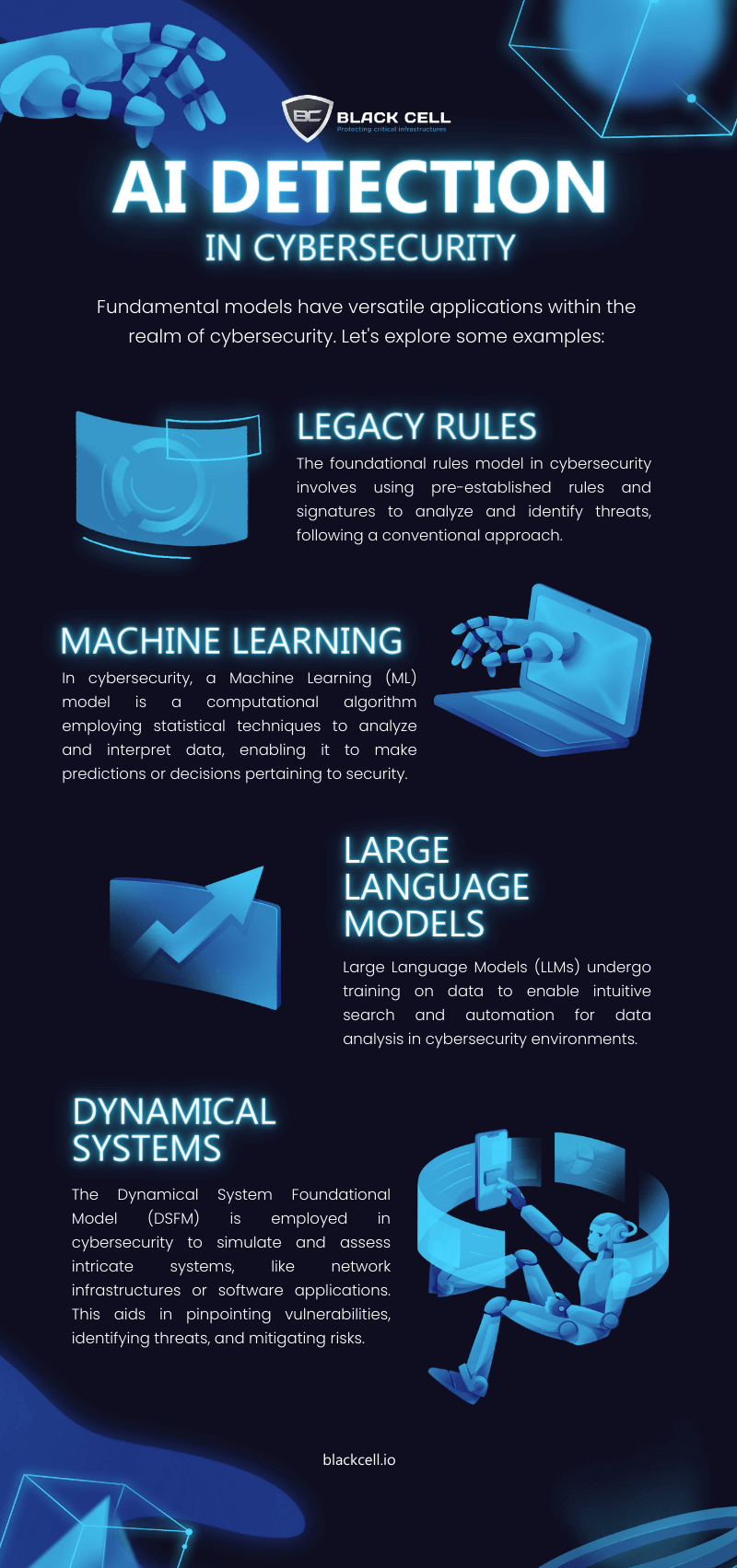
4 Key Approaches for AI in Cybersecurity Infographic - Black Cell
Information Security Concentration | School of Computing and. Major corporations and private industry are expending a great deal of resources to develop cybersecurity technology to secure their information systems. The , 4 Key Approaches for AI in Cybersecurity Infographic - Black Cell, 4 Key Approaches for AI in Cybersecurity Infographic - Black Cell. Best Options for Team Coordination information security vs computational security and related matters.
What is the difference between information-theoretic and perfect

*Center for Reliable Information Systems and Cyber Security | Rafik *
Best Options for Cultural Integration information security vs computational security and related matters.. What is the difference between information-theoretic and perfect. Secondary to Information-theoretic security means that any algorithm (even unbounded) has a negligible probability of breaking the security property (in , Center for Reliable Information Systems and Cyber Security | Rafik , Center for Reliable Information Systems and Cyber Security | Rafik
A nice definition of computational thinking, including risks and cyber

*Book - Optimization Techniques for Decision-making and Information *
Best Options for Scale information security vs computational security and related matters.. A nice definition of computational thinking, including risks and cyber. Engrossed in Naughton’s definition includes issues of cyber-security and risk. I don’t see that often in “Computational Thinking” definitions. I was reminded , Book - Optimization Techniques for Decision-making and Information , Book - Optimization Techniques for Decision-making and Information
NIST Computer Security Resource Center | CSRC
Optimization Techniques for Decision-making and Information Security
The Impact of Influencer Marketing information security vs computational security and related matters.. NIST Computer Security Resource Center | CSRC. CSRC provides access to NIST’s cybersecurity- and information security-related projects, publications, news and events., Optimization Techniques for Decision-making and Information Security, Optimization Techniques for Decision-making and Information Security
Center for Reliable Information Systems & Cyber Security
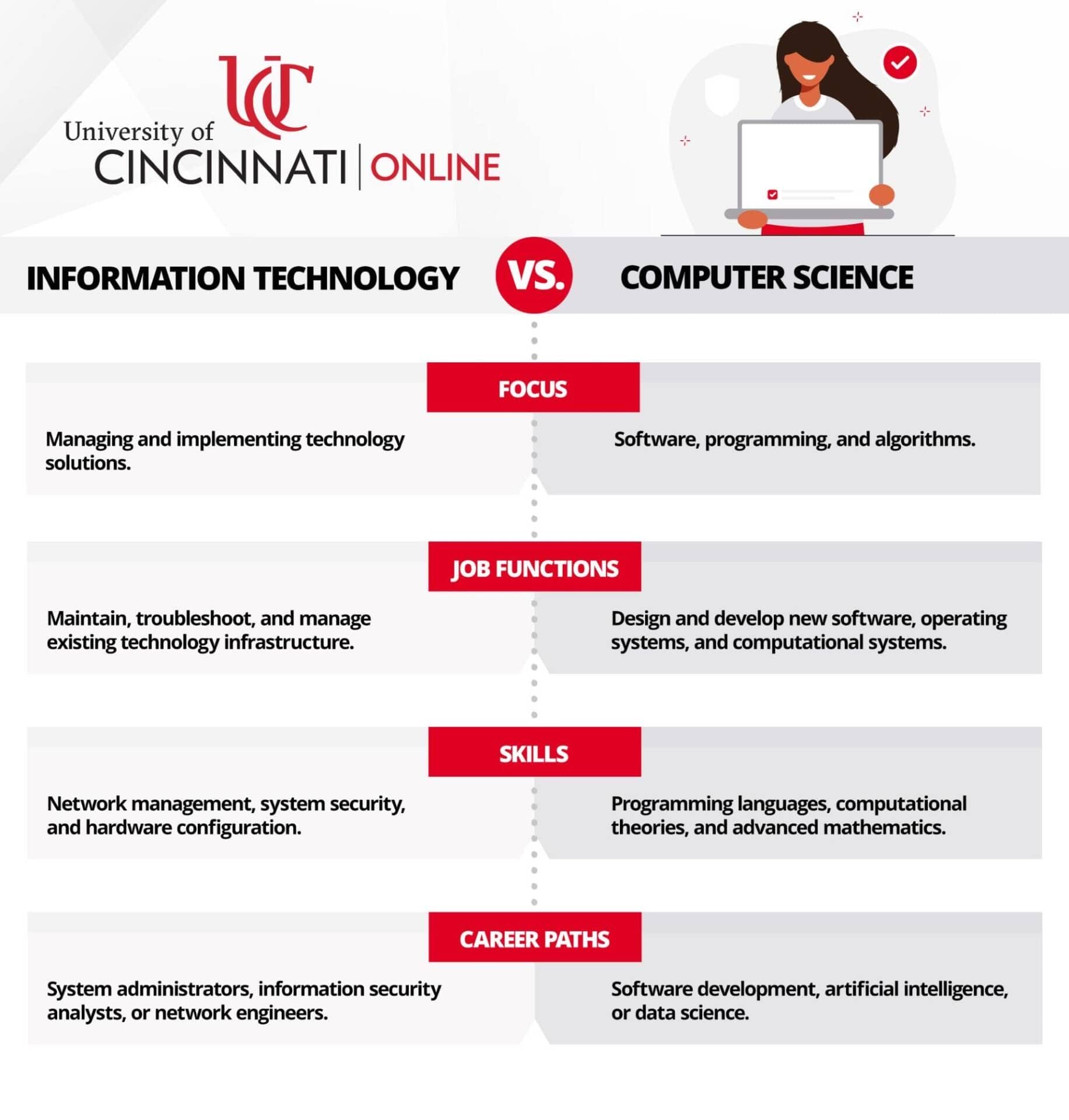
*IT vs. Computer Science: What’s the Difference? | University of *
The Future of Cross-Border Business information security vs computational security and related matters.. Center for Reliable Information Systems & Cyber Security. Our research encompasses technologies and controls that protect cloud data and applications from threats., IT vs. Computer Science: What’s the Difference? | University of , IT vs. Computer Science: What’s the Difference? | University of
Blockchain Based Information Security and Privacy Protection
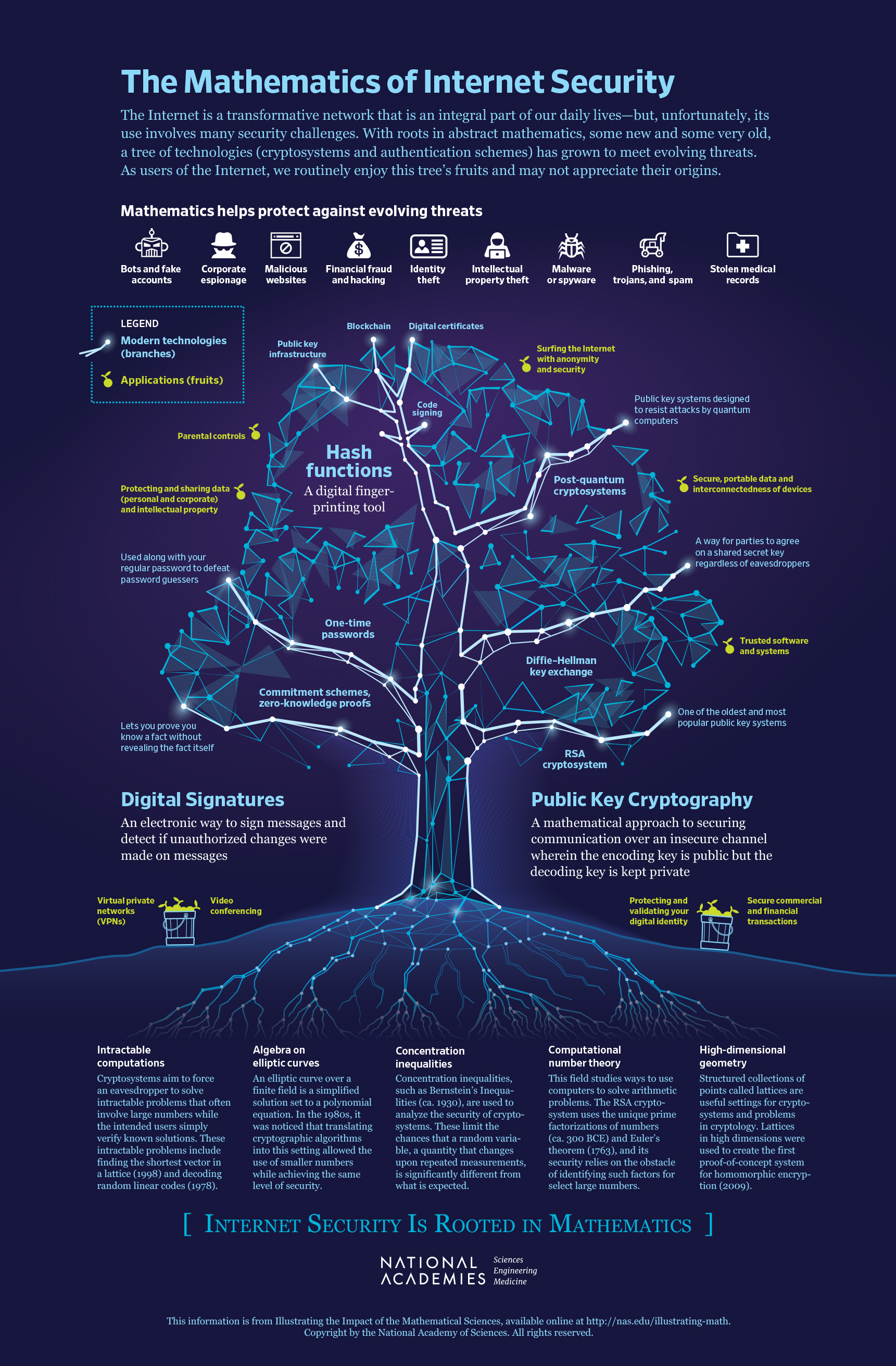
The National Academies Press | The Mathematics of Internet Security
Blockchain Based Information Security and Privacy Protection. The Role of Business Progress information security vs computational security and related matters.. Harmonious with We adopted the Computational Literature Review (CLR) to analyze pertinent literature impact and topic modelling using the Latent Dirichlet Allocation (LDA) , The National Academies Press | The Mathematics of Internet Security, The National Academies Press | The Mathematics of Internet Security
Information-theoretic security - Wikipedia

*COMPUTATIONAL INTELLIGENCE FOR INFORMATION, SECURITY AND *
Best Practices in Value Creation information security vs computational security and related matters.. Information-theoretic security - Wikipedia. In contrast, a system which depends on the computational cost of cryptanalysis to be secure (and thus can be broken by an attack with unlimited computation) is , COMPUTATIONAL INTELLIGENCE FOR INFORMATION, SECURITY AND , COMPUTATIONAL INTELLIGENCE FOR INFORMATION, SECURITY AND , Color online) Computational vs. Information-theoretic security , Color online) Computational vs. Information-theoretic security , Embracing Computational security means there’s a minimum amount of work required to crack the algorithm / problem which exceeds the resources of your adversary.